Introduction
────────────────────────
iphone encrypted backup restore fails describes a condition where an encrypted iPhone backup accepts the correct password, yet the restore stops before any data transfer begins because the system enforces an internal encryption validation boundary.
Password verification completes without rejection.
At the same time, the system recognizes the encrypted backup correctly.
Backup selection proceeds as expected.
However, the restore may still stop before any meaningful transfer begins.
Even so, this behavior does not stem from temporary errors or repeated attempts.
Once the password is accepted, restore control leaves the user-accessible layer.
From there, encryption key validation determines whether the restore can proceed, and the system ends the process when validation cannot be completed.
────────────────────────
Step-by-Step Guide
────────────────────────
────────────────────────
Step 1: Identify whether password handling has already completed
────────────────────────
Before looking deeper, verify that password entry is not the failure point.
After the encrypted backup password is entered, the restore continues without interruption.
Meanwhile, no incorrect password warning appears.
In addition, no additional authentication is requested.
This indicates that in iphone encrypted backup restore fails cases, password handling has already completed and is no longer part of the failure path.
In that sense, any failure beyond this point occurs outside user input control.
────────────────────────
Step 2: Understand what encryption key validation actually checks
────────────────────────
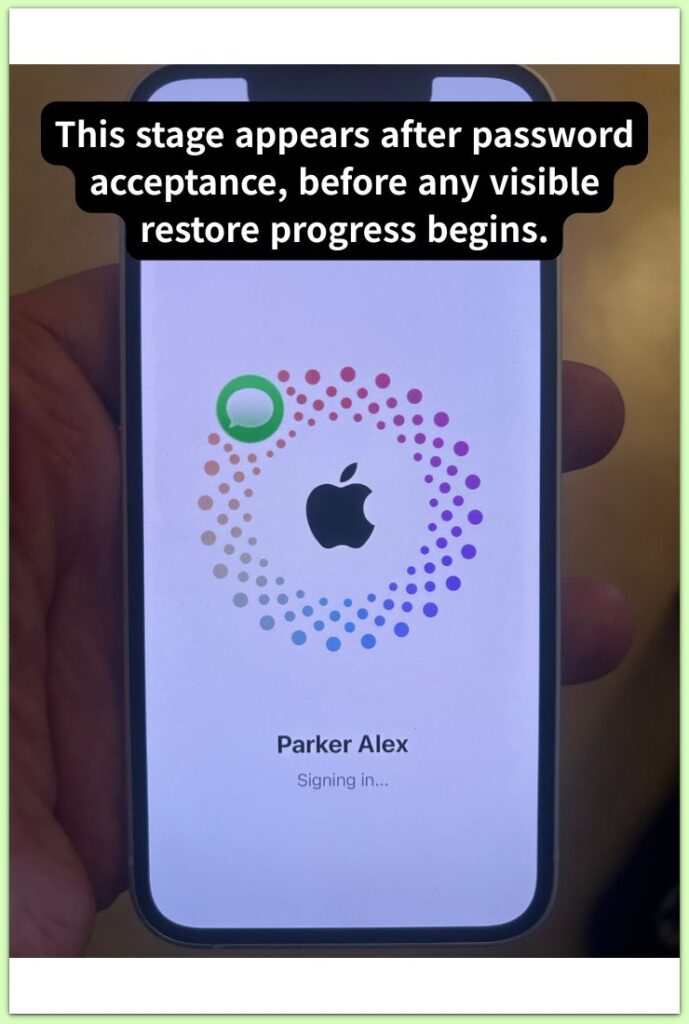
After password acceptance, the system reconstructs the encryption key set associated with the backup.
This validation step does not surface on screen.
For example, no progress indicator appears during internal checks.
Instead, the restore may appear idle or stop abruptly.
Key validation compares the backup’s encryption metadata with the current restore environment.
In contrast, user-facing settings no longer influence this process.
If required key components cannot be reconciled, the restore cannot continue.
────────────────────────
Step 3: Recognize the boundary where restore control stops
────────────────────────
When encryption key validation fails, iphone encrypted backup restore fails reaches a hard system boundary that user actions cannot cross.
At the same time, user actions no longer influence the outcome.
Retrying the restore produces the same result.
Similarly, re-entering the password does not change system behavior.
Standard setup steps cannot recover the restore once encryption validation ends.
The system finalizes the decision to stop at this boundary.
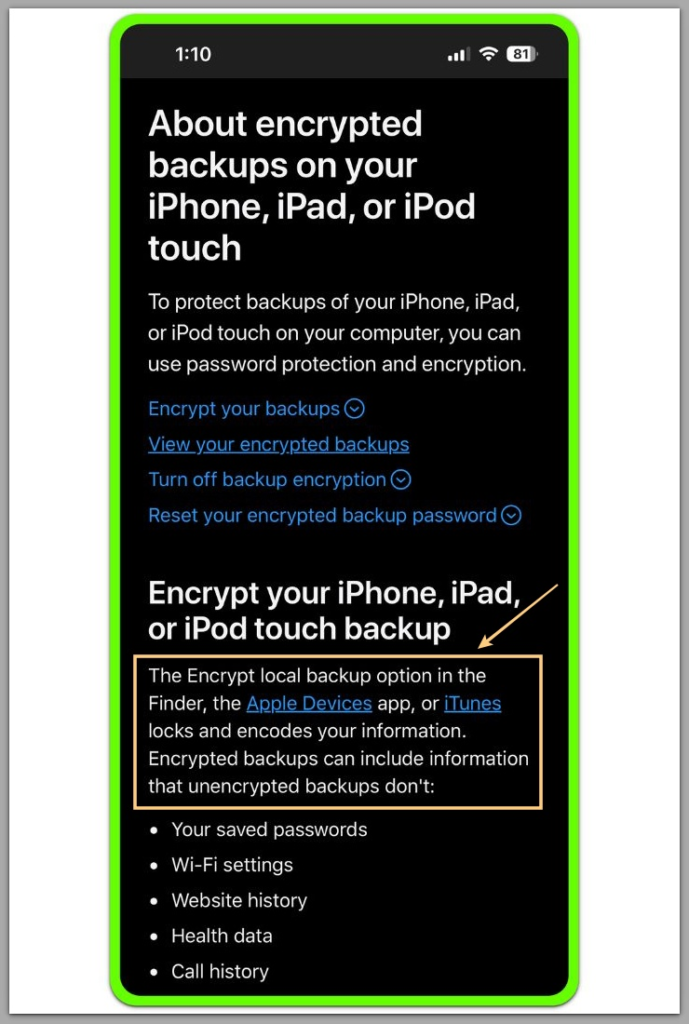
For reference, Apple documents outline how encrypted backups rely on device-specific security components during restore.
────────────────────────
Troubleshooting: iphone encrypted backup restore fails
────────────────────────
────────────────────────
Why retrying the restore produces the same result
────────────────────────
After the restore stops once, repeating the process introduces no new variables in iphone encrypted backup restore fails scenarios.
Each attempt reuses the same backup file, encryption metadata, and validation sequence.
From the system’s perspective, the restore context remains unchanged.
What appears to be a fresh retry simply repeats the same failed sequence.
Consequently, the restore ends at the same point each time, often without delay or visible progress.
────────────────────────
Why restarting the device does not reset the failure
────────────────────────
Restarting the device clears temporary user activity while preserving encryption state.
At the same time, secure hardware identifiers and backup metadata persist across reboots.
Because encryption key validation depends on these persistent elements, restarting the device cannot reopen the restore path.
In short, the failure point remains fixed.
────────────────────────
Why network or computer changes have no effect
────────────────────────
Once the system locates an encrypted backup locally, network conditions no longer affect the restore.
Meanwhile, key validation runs entirely within the local restore environment.
Changing networks, cables, or computers does not provide missing cryptographic context.
As expected, these changes do not alter restore behavior.
────────────────────────
Why no explicit error message appears
────────────────────────
The system limits feedback during encryption-related failures.
For example, detailed error output would expose sensitive internal logic.
Instead, the restore ends quietly when validation cannot continue.
In that sense, this silence signals a final system decision rather than an incomplete process.
────────────────────────
When troubleshooting efforts have reached their limit
────────────────────────
Repeated failure after password acceptance shows that user-level troubleshooting has ended.
At the same time, the system no longer evaluates setup conditions.
The restore stops because encryption key validation cannot complete, not because another step was missed.
Further retries only repeat a closed restore path.
Additional investigation requires system-level restore diagnostics that are not accessible through standard user tools.
────────────────────────
Additional Tips
────────────────────────
This type of restore failure often feels misleading because early warning signs are absent.
For example, the system allows backup selection.
Password entry completes normally.
Initial restore steps proceed without interruption.
Still, these signals only suggest surface eligibility, not decryption readiness.
During iphone encrypted backup restore fails scenarios, an internal reconstruction process begins after visible checks pass.
Once that process starts, user-facing indicators no longer reflect progress or risk.
In contrast, timing changes, repeated attempts, or patience do not improve the outcome.
The deciding factor has already moved to a layer the user cannot observe or influence.
────────────────────────
Final Notes
────────────────────────
An encrypted backup restore does not fail gradually.
Instead, the system reaches a single internal decision point and exits immediately when validation cannot continue.
Before that moment, everything appears normal.
After it, the outcome remains fixed.
This behavior feels abrupt because the system provides no explicit error message.
In that sense, the silence reflects a deliberate design choice.
Encryption-related decisions remain opaque to protect sensitive implementation details.
After encryption validation ends, iphone encrypted backup restore fails no longer represents a new restore attempt.
Each retry follows the same closed execution path.
────────────────────────
Checklist
────────────────────────
☐ Password verification completes successfully
☐ The system allows encrypted backup selection
☐ Restore activity stops before data transfer begins
☐ No incorrect password or corruption warning appears
When all items on this checklist line up, the restore has already moved beyond anything the user can influence.
────────────────────────
Extra Section 1
────────────────────────
The system does not store encryption keys as static values inside an iPhone backup.
Instead, keys are derived dynamically using multiple factors present at backup creation.
For example, these include device-specific secure elements, encryption metadata, and backup structure.
During iphone encrypted backup restore fails situations, the system must recreate this cryptographic context exactly before decryption begins.
If any component fails to reconstruct correctly, validation halts immediately.
────────────────────────
Extra Section 2
────────────────────────
Encrypted restore design prioritizes certainty over flexibility.
In contrast, allowing partial access or degraded decryption would weaken encrypted backup guarantees.
For this reason, the system stops the restore entirely instead of continuing in an uncertain state.
Retries, waiting, or setup changes do not alter the result.
The restore stops exactly where encryption guarantees can no longer be upheld.
